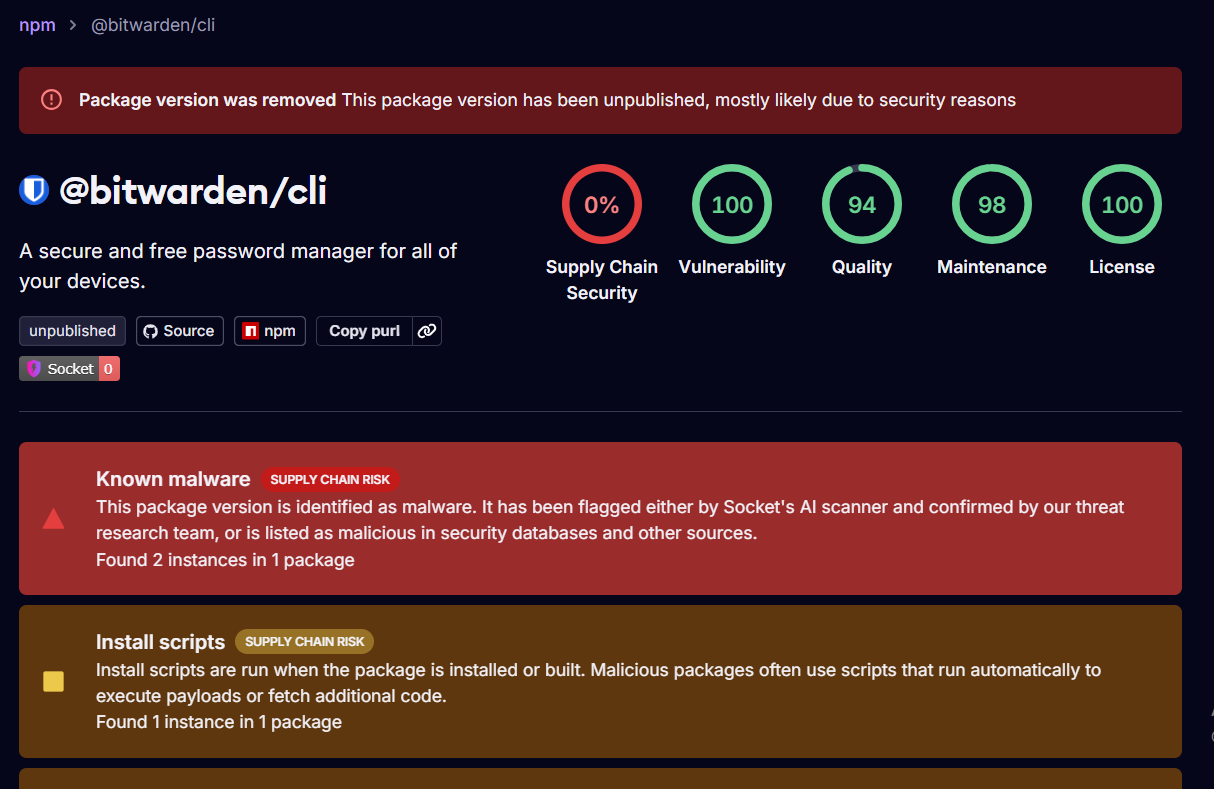
A malicious version of Bitwarden’s CLI tool was briefly published on npm before being quickly removed, after security researchers flagged it as part of a supply chain attack targeting developers.
The affected version, 2026.4.0, was available for a short period of time but included code designed to extract sensitive data from developer environments rather than targeting end users directly.
A Compromise in the Supply Chain
Early analysis suggests the malicious package was introduced through a compromised build or release process, rather than a vulnerability in Bitwarden’s core software.
This type of attack — often referred to as a supply chain attack — focuses on injecting malicious code into trusted tools and libraries, allowing attackers to reach a large number of systems indirectly.
What the Malware Was Doing
Unlike traditional attacks aimed at stealing user data, this payload was designed to target developers and infrastructure.
Security findings indicate the package attempted to access:
- Authentication tokens and API keys
- SSH credentials
- Environment variables used in CI/CD pipelines
By collecting this information, attackers could potentially gain access to repositories, cloud services, and other internal systems.
Limited Exposure Window
The malicious version was available for only a short time before being taken down, reducing the overall impact.
Bitwarden has stated that there is no evidence of compromised user vaults or leaked password data, and the incident appears to be limited to the distribution channel rather than the product itself.
Why This Matters
This incident highlights a growing shift in cyberattacks. Instead of targeting applications directly, attackers are increasingly going after the tools developers rely on to build and deploy software.
Developer environments often contain high-value secrets, making them a prime target for attackers looking to move laterally across systems.
What Developers Should Do
Anyone who installed the affected version should take immediate steps to secure their environment:
- Remove or downgrade the affected package
- Rotate all API keys and tokens
- Review recent activity in repositories and cloud services
Even short-lived supply chain incidents can have lasting consequences if compromised credentials are reused or left active.
Sources & References
- Socket.dev — Package Analysis
- Security research reports on npm supply chain attacks
This article was written by DigitalEscapeTools based on security analysis and publicly available research.